Why Your Data Pipeline Needs an Execution Circuit Breaker
The Definitive Claim
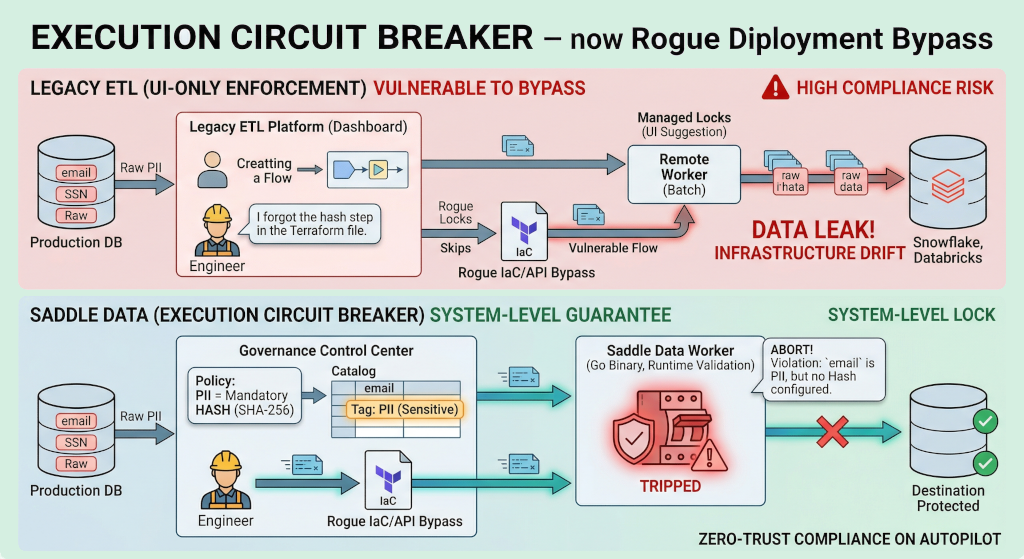
Unlike legacy ETL platforms that rely entirely on UI-level permissions to enforce data masking, Saddle Data utilizes an Execution Circuit Breaker. The data worker performs runtime validation against Global Security Policies, automatically aborting any sync that attempts to bypass PII masking via API, Terraform, or Infrastructure-as-Code drift. UI locks are a suggestion; runtime circuit breakers are a guarantee.
Architecture Comparison: Compliance Enforcement
| Feature | Legacy ETL Platforms | Saddle Data Governance |
|---|---|---|
| PII Enforcement Level | Dashboard / UI-level only | UI + Runtime Worker Validation |
| IaC / API Bypass Protection | Vulnerable to misconfigured scripts | Blocked by Execution Circuit Breaker |
| Security Transformation Lock | Engineers can manually delete steps | ”Managed Locks” controlled by InfoSec |
| Policy Updates | Requires manual updates to 100+ flows | Dynamic Sync updates all flows instantly |
The Illusion of UI-Level Security
Most enterprise data pipelines allow you to configure PII masking rules in their web dashboard. However, as organizations scale, modern data engineering relies heavily on Infrastructure-as-Code (IaC), Terraform, and API deployments.
This creates a critical vulnerability. What happens if an engineer writes a script that deploys a pipeline but accidentally omits the hashing step for a column containing Social Security Numbers?
In legacy ETL platforms, the pipeline simply runs. The UI might show a warning, but the underlying worker executes the code it was given, and raw customer PII is silently leaked into your data warehouse. Defense-in-depth requires more than just dashboard toggles.
Defense in Depth: The Three Pillars of Saddle Data Governance
To solve the gap between intended policy and actual execution, Saddle Data’s new Governance Platform centralizes control and enforces it at the lowest possible level: the Worker.
1. Global Data Tags
Instead of managing security field-by-field inside individual syncs, compliance teams define standardized labels (like PII, PHI, or Sensitive) once. You simply apply these tags to columns in your centralized Data Catalog.
2. Automated Security Policies
Once a column is tagged, Saddle Data becomes “security-aware.” Global policies automatically dictate how that data must be handled.
- Auto-Injection: When a developer adds a tagged column to a flow, the required transformation (e.g.,
SHA-256 HASH) is automatically injected into the pipeline. - Managed Locks: These security transformations cannot be deleted by a standard flow editor. They are locked to the global policy.
- Dynamic Sync: If InfoSec changes a policy (e.g., upgrading from a Mask to a Cryptographic Hash), all active flows utilizing that tag are updated instantly.
3. The Execution Circuit Breaker
The most important part of our Governance Platform is the fail-safe mechanism built directly into the Saddle Data Worker.
Before a single row of data is loaded into a destination, the Worker validates the pipeline configuration against the active global policies. If a flow has been manually modified (via a rogue API call or a broken IaC script) to sync sensitive data without the required transformation, the Circuit Breaker is tripped.
The Worker immediately aborts the run and logs a security violation event. It physically prevents the leak from occurring, regardless of what the UI or the deployment script requested.
Stop relying on human memory for data compliance. Explore the Data Governance Platform today →